From Findings to Business Risk
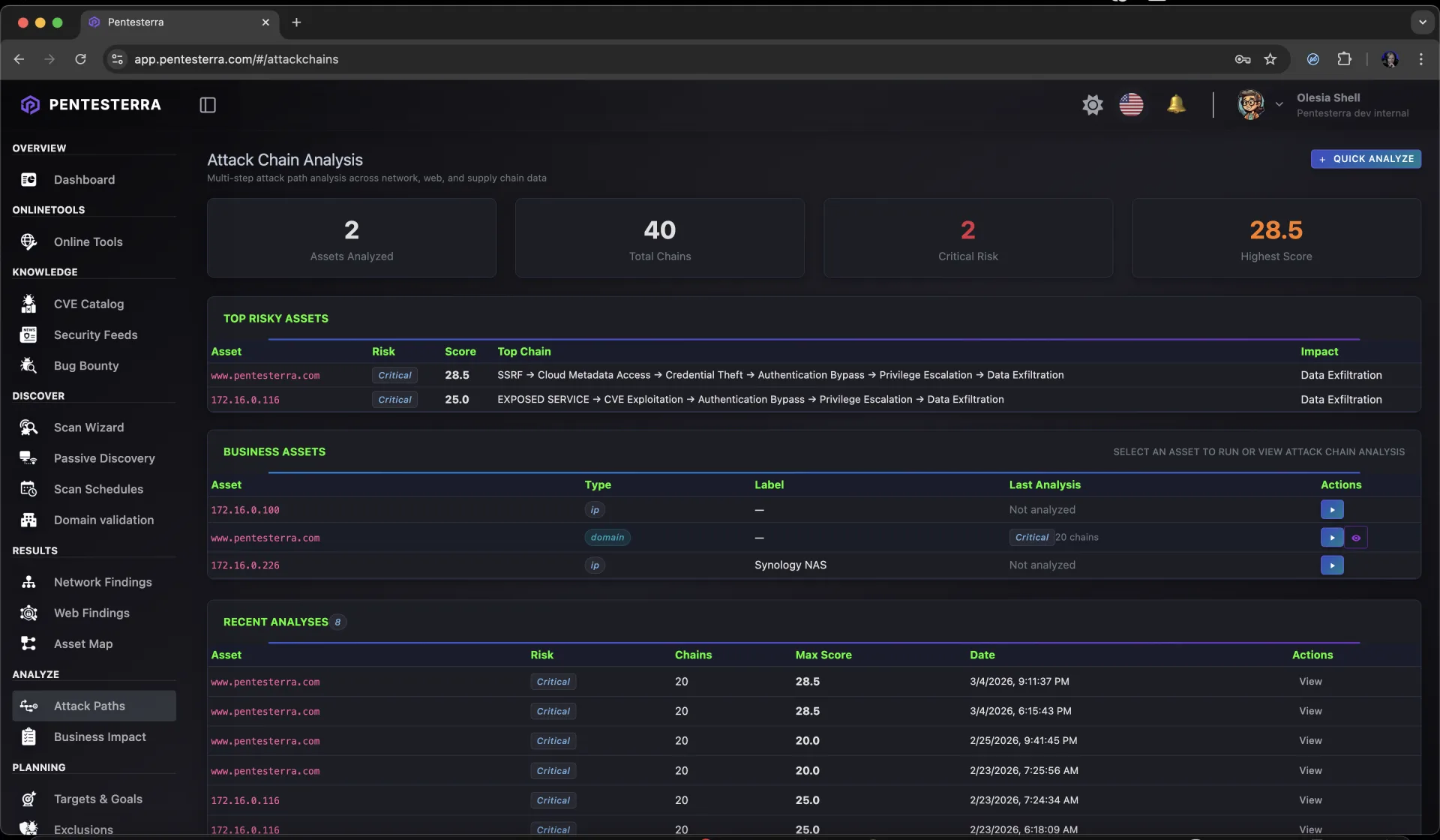
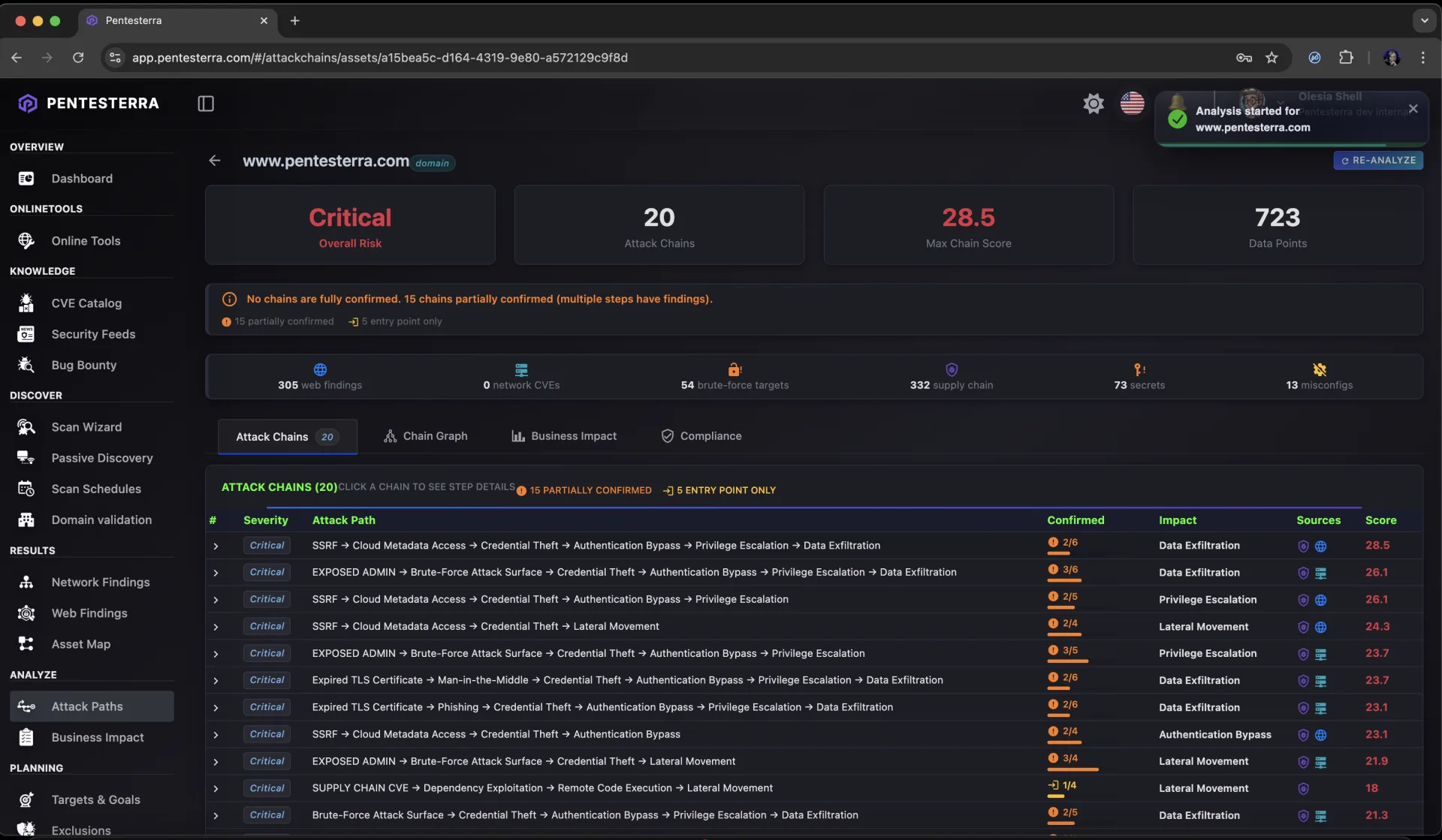
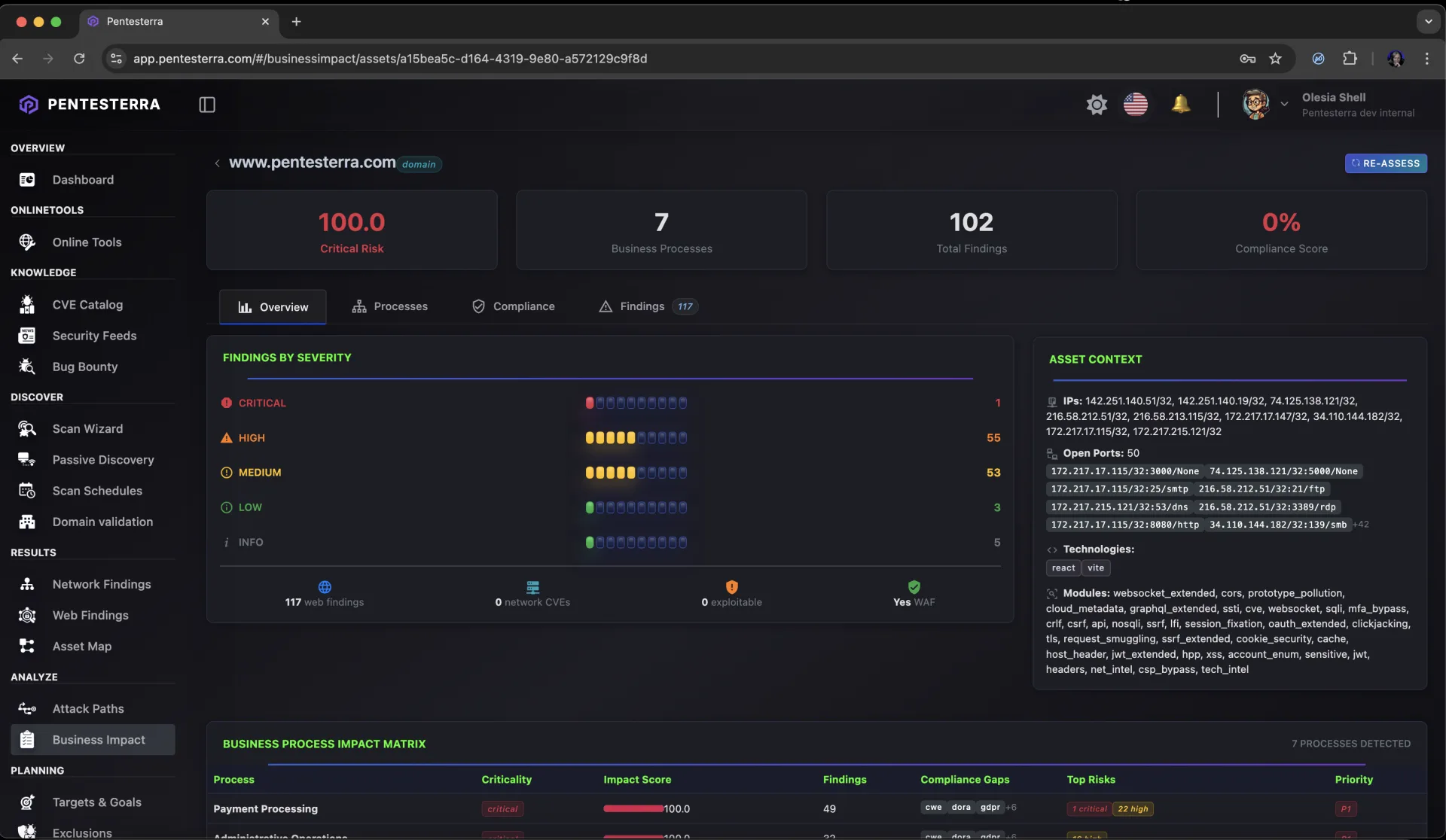
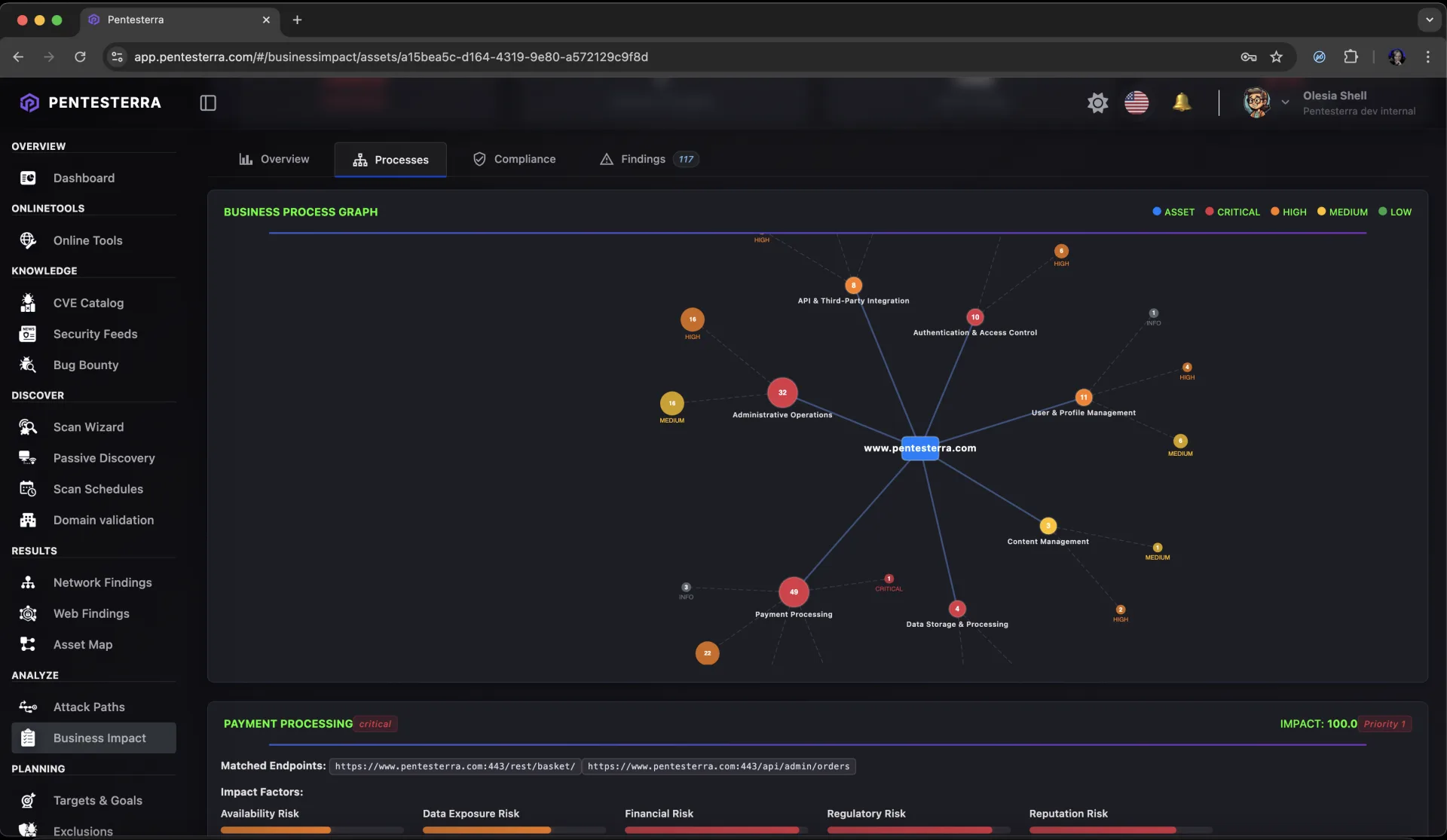
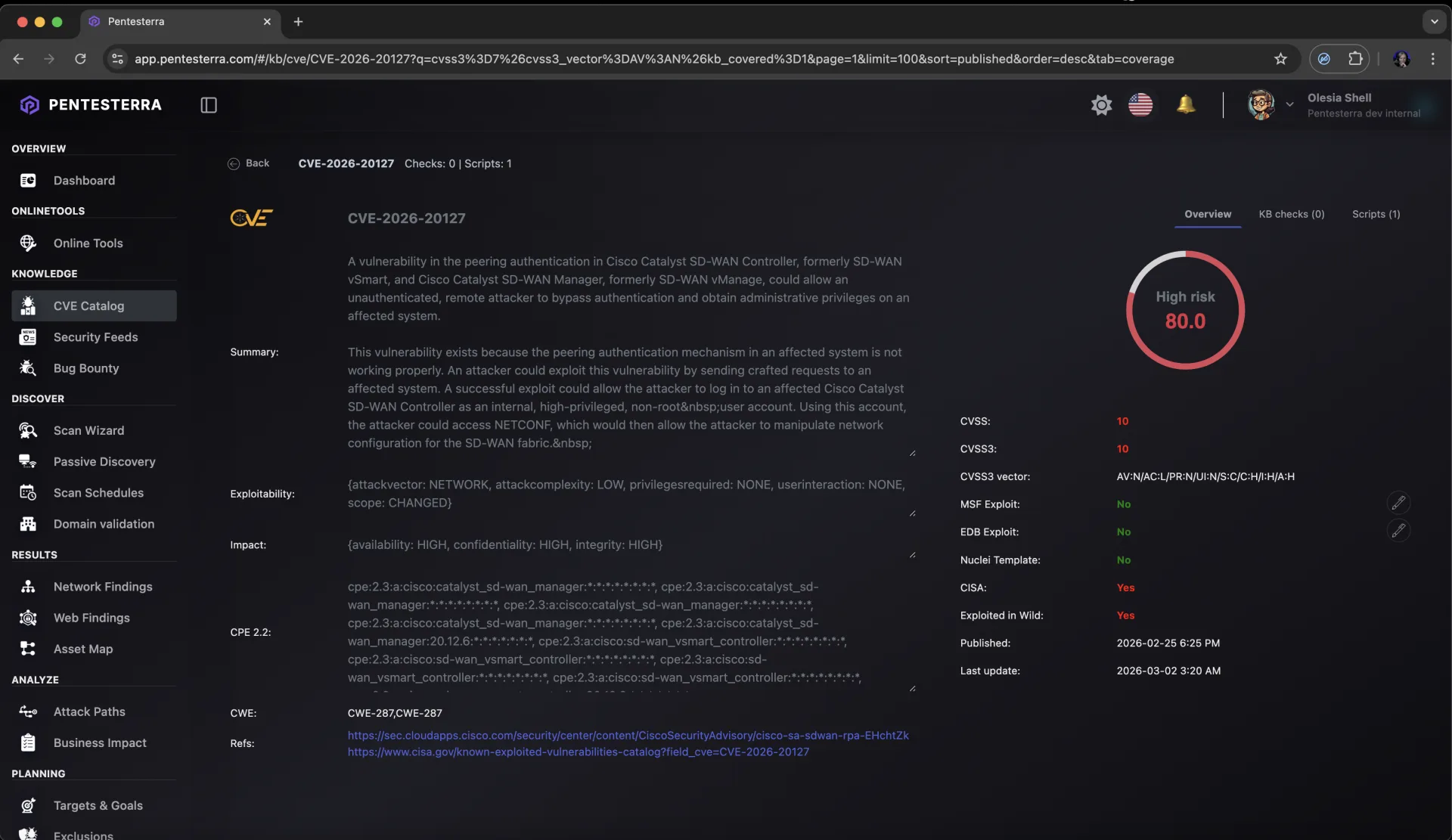
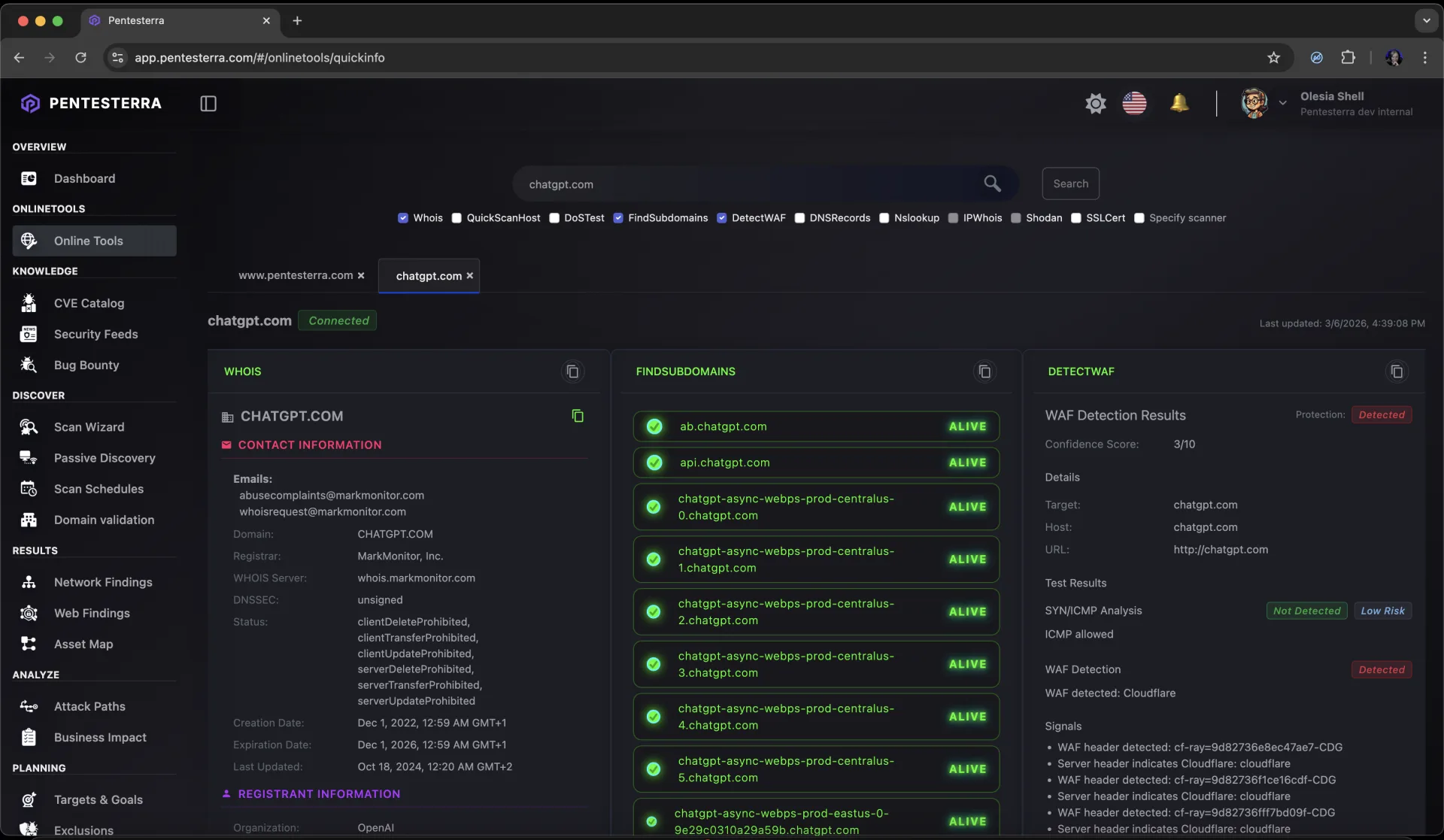
Verified findings are correlated into multi-step attack chains - modelling how a real attacker moves through your environment, what they can reach, and what they can extract. Business processes, logic flaws, and compliance gaps are part of the analysis.
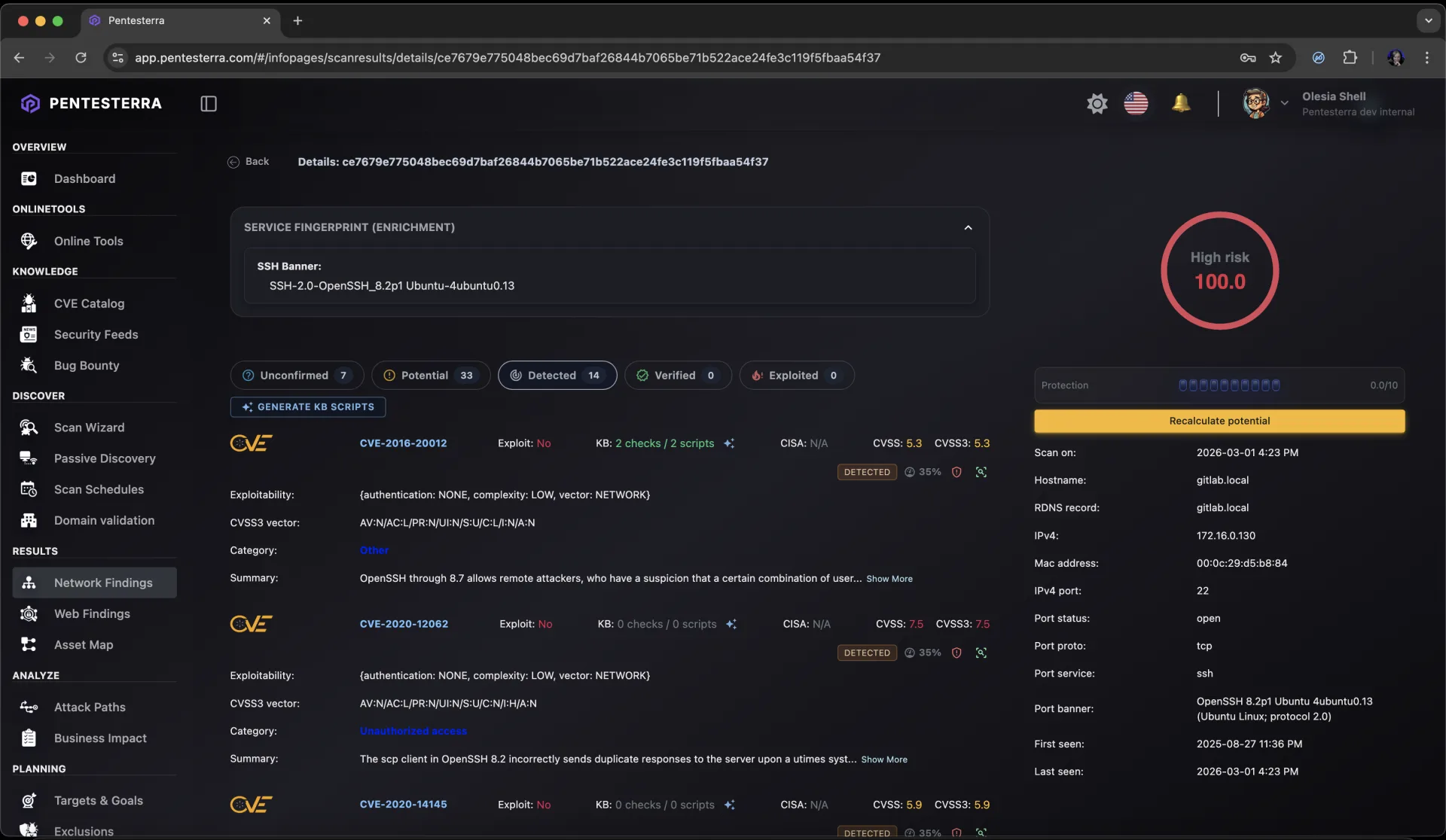
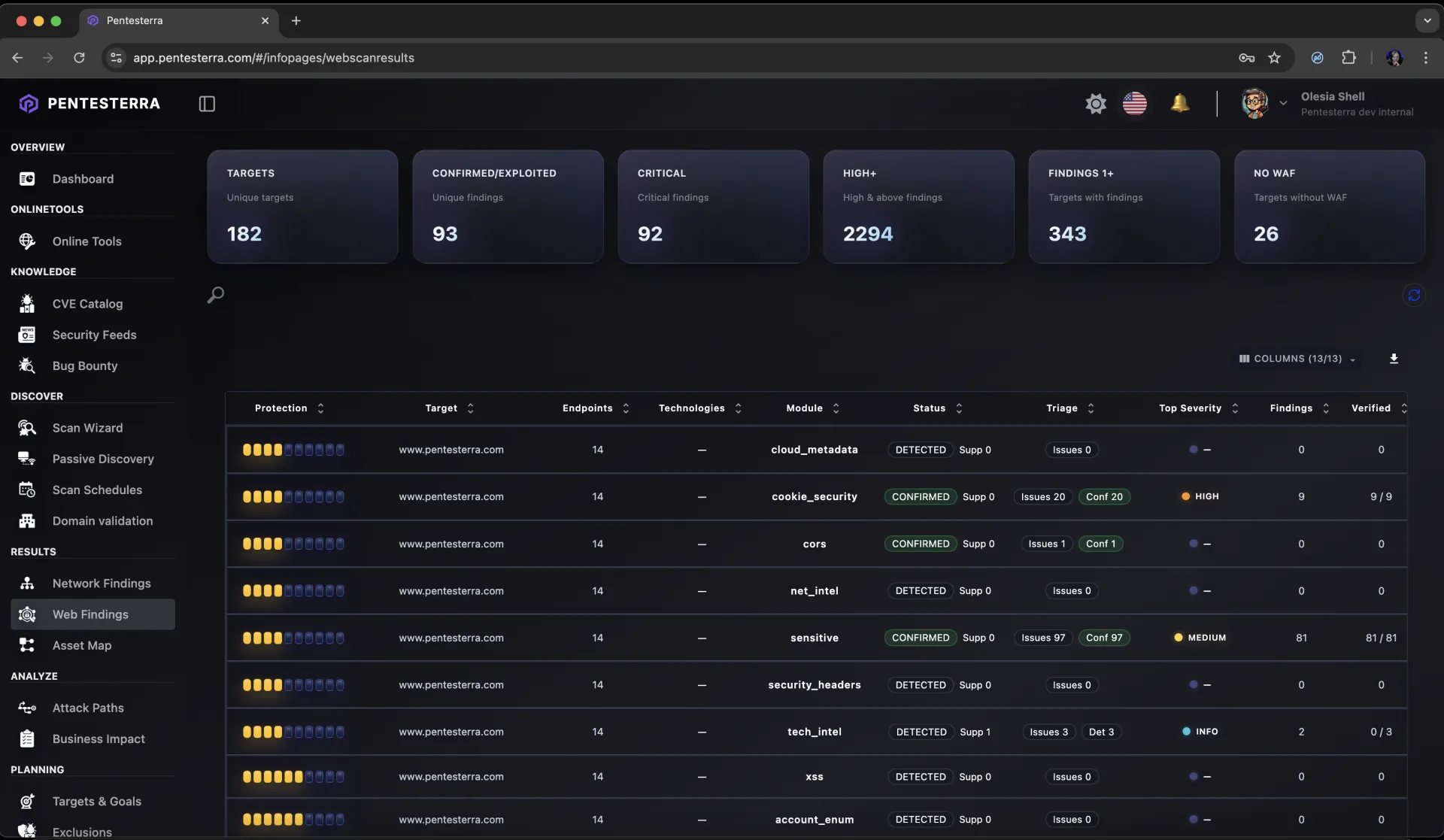
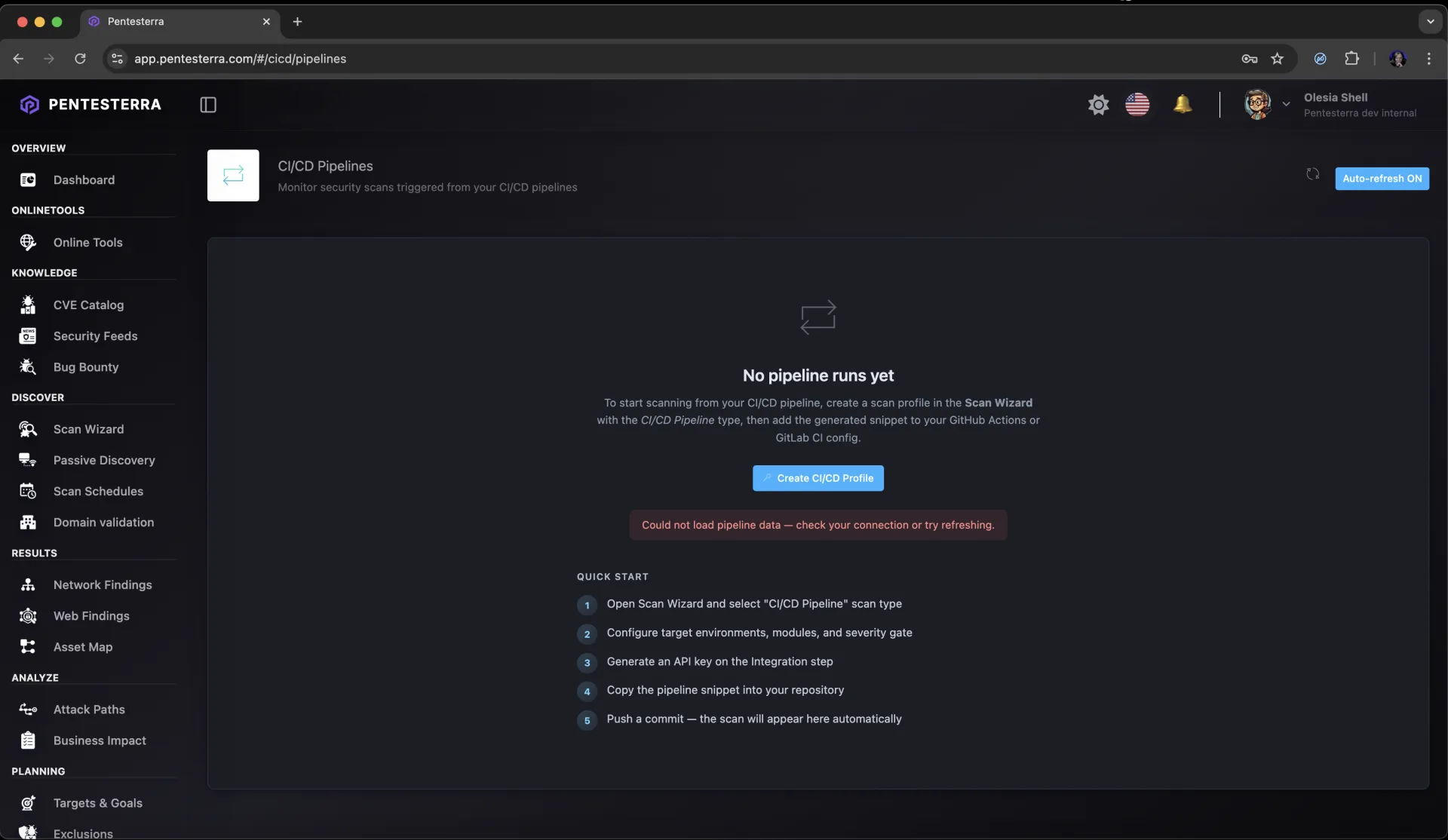
- Attack Chain Analysis - Findings from web, network, and CI/CD sources are combined into directed kill-chain graphs. Each chain shows progression from initial access to full compromise - with blast radius (how many hosts are reachable) and what an attacker can extract at every step.
- Business Process & Logic Impact - Chains are mapped to affected business processes and detected logic vulnerabilities: payment flows, identity & access, API logic, CI/CD pipelines. Each finding is scored by the business function it threatens and the financial risk it carries.
- Compliance Mapping - Automated mapping to OWASP Top 10, PCI-DSS, GDPR Art. 32/33, NIST 800-53, and ISO 27001. Compliance gaps are derived from actual verified findings - not self-assessments.